[fancy_header3 variation=”orange”] Use case for MPLS in the Enterprise for PCI Compliance[/fancy_header3]
MPLS is today’s only form of scalable network virtualization we have for now. I personally think the promise of something called SDN will move into that space soon but until then, we need network virtualization. PCI is a joke. It is a racket by Visa and banks to spread fear without any brains behind the architecture. PCI DSS v2.0 soon to be v3.0 is on of the few technological security documents that clearly states the requirements. Path Isolation is very clear for the network architect to build a design around.
That happens to be the bread and butter of MPLS as it has been used for well over a decade by service providers to provide multi tenant virtualized networks. Virtual logical and scalable networks overlaid on top of a single physical network.
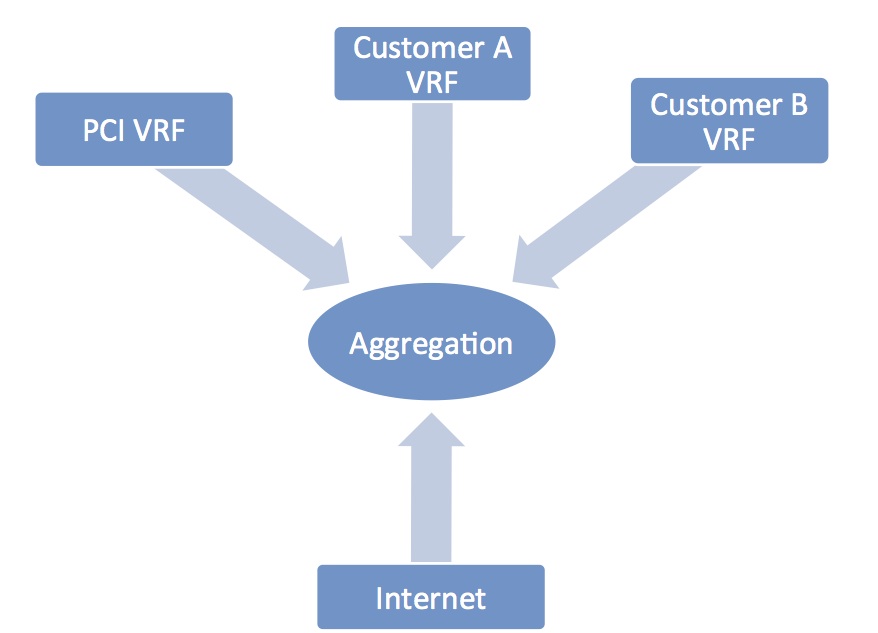
Figure 1 MPLS/VPNs create logical routed containers to apply meny types of policy.
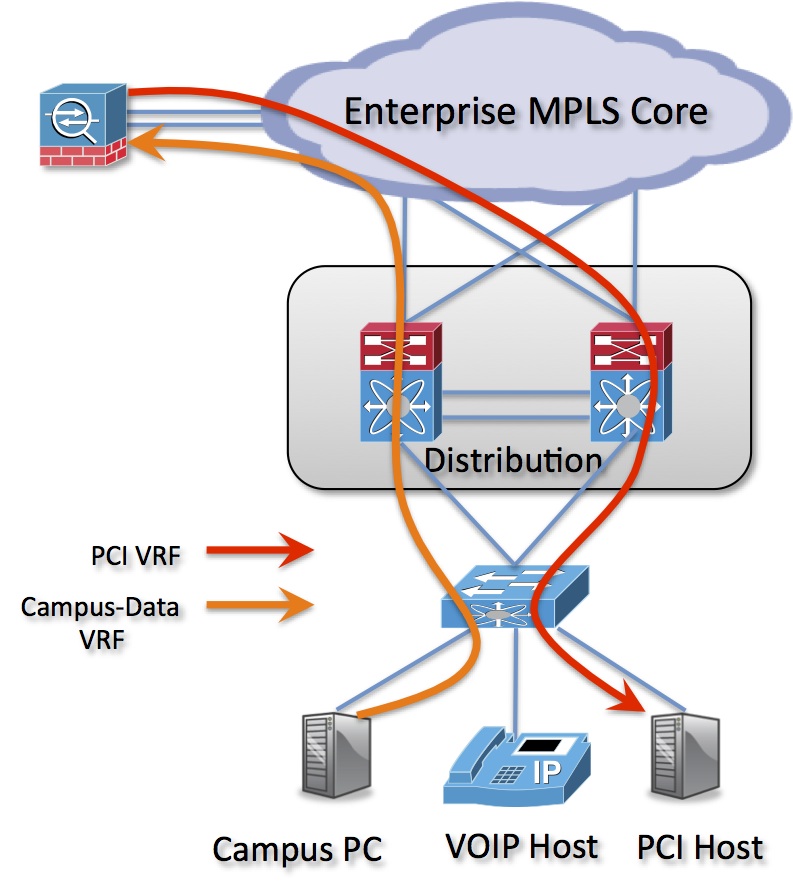
Figure 2 Layer 2 traffic from access to distribution is isolated using typical 802.1Q trunking. There is a different Vlan ID associated to each VRF south of each pair of distribution routers. Vlans maintain the layer2 bridging or broadcast domain isolation. In traditional and still the majority of Enterprise networks that is the extent of path isolation. The problem is that layer2 bridging does not scale.
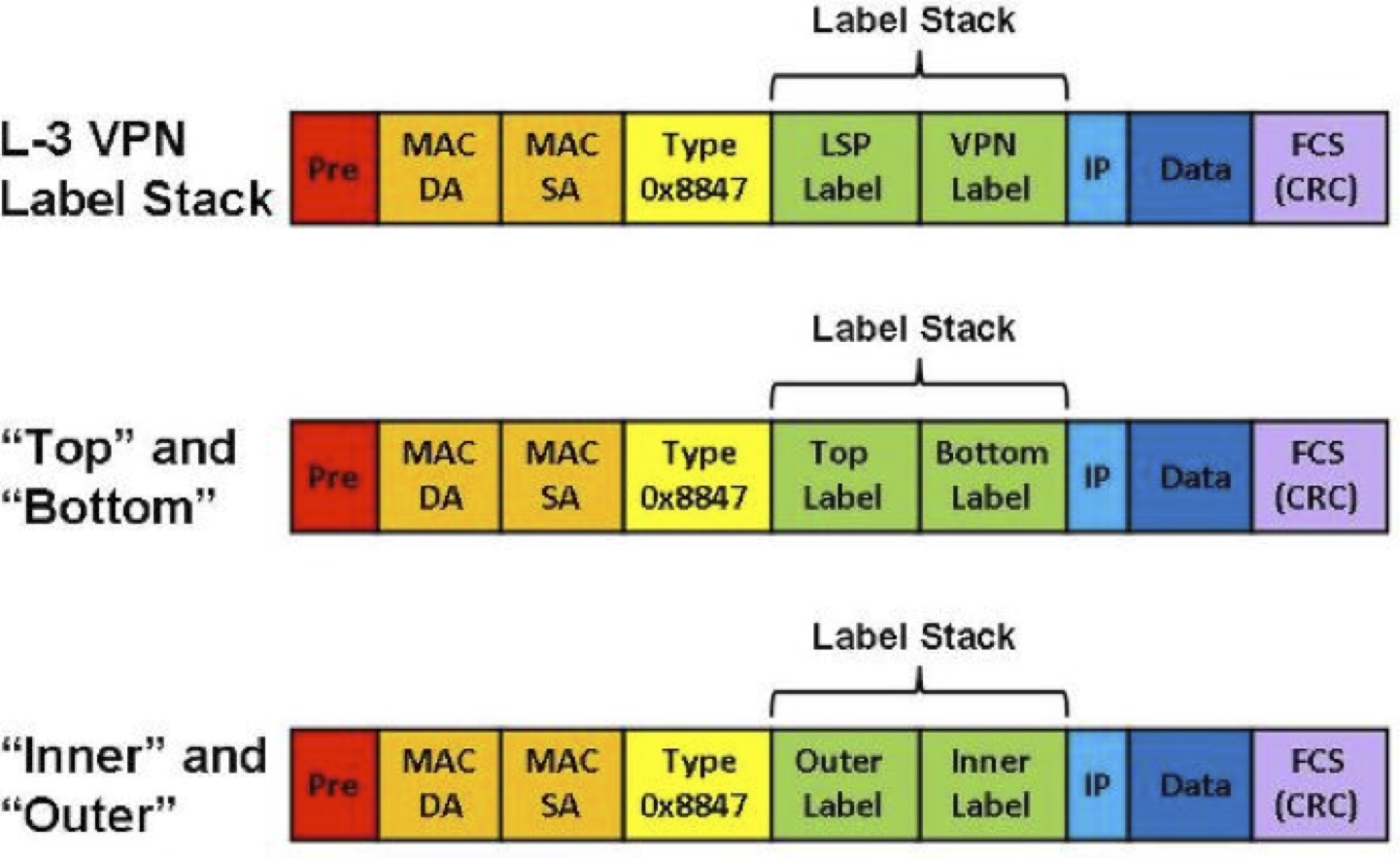
Figure 3. MPLS Label Stacking.
Once a bridged Ethernet frame reaches it’s Layer 3 demarcation, traffic is logically separated in the core with MPLS encapsulation/framing or “tag/label switching”. Labels are inserted in between the Ethernet header (Layer2) and IP header (Layer3) thus MPLS is often referred to as Layer 2 1/2. A label stack is imposed into the Ethernet frame at the ingress label switch router (LSR). The inner label (e.g. PCI, mc-data, VOIP, campus-data) is preserved throughout the MPLS cloud and while the outer tag is pushed on ingress, swapped traversing the core and both are popped on the egress router. That inner label is the path isolation between two security zone, customers etc.
For a vanilla MPLS configuration in IOS here is a link .

Before you do so you’d probably better review the position of PCI as to the “Private” or “Public” characteristics of MPLS. See http://selfservice.kb.net/article.aspx?article=8705&p=81
Just be prepared that this issue is unlikely to go away. Plan on strong link encryption over MPLS.
Brent,
Typically it would be the carrier’s customer that gets caught here. The carriers have typically resisted doing this although that may be changing.
Forget the traffic. Consider the MLPS router at the customer’s edge. Some are exposed on the Internet and managed that way. Some by telnet. Now what could someone do with control of one or more of those?
The audits aren’t public documents. The best you can usually do is to see if the carrier is on one of the compliant service provider lists (or not) and then find out what that services that certification actually covers.