The Brocade acquisition of Vyatta was announced today. On the surface Vyatta is functionality we have in today’s routers to load in VMs or on physical gear as a software router. It is complete with IGPs, EGPs, QOS, PBR, Crypto (no MPLS) and about everything else you find in a traditional router. Vyatta is not a vSwitch, it is routing functionality in x86. While being delivered in software ,almost everything I see is leveraging our existing bag of networking protocols and encapsulations to integrate into the network along with service provisioning in an on demand fashion. They do mention the ability to accommodate OpenFlow. I would imagine as aggressive as Brocade is on SDN that will be in the works day one, if it is not already in the pipeline.
I snipped some pictures from there documents and grabbed some highlights that might save someone some research time. Think, routers in x86 and how you can use that to manage VM L3 traffic with PBR, QOS and whatever else programmatically in the near term. In the long term sprinkle in whatever mechanism (if) the industry decides to use as its wire protocol for control plane extraction, e.g. OpenFlow, MPLS etc.
Per the Vyatta website is a snippet of how they see SDNs role:
Software-Defined Networking (SDN) allows you to design, provision and scale Layer 2 (L2) networks to meet rapidly changing business needs. Vyatta’s virtual routers, virtual firewalls and VPNs enable you to connect the L2 SDN “islands” to each other, as well as the broader infrastructure.
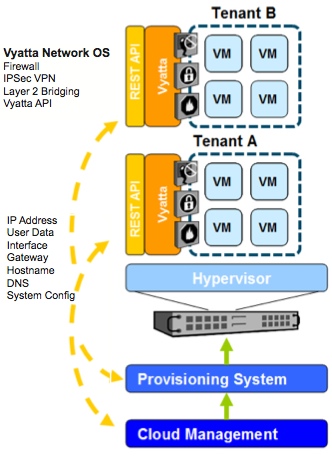
Vyatta for Virtualized Environments
Vyatta supports the following hypervisors VMware, Citrix Xen and XenServer and Red Hat KVM. This means they deliver their software images that can run as a VM or on physical host. This does not mean they have a vSwitch product. These are x86 routers. The vSwitch integration will come from Open vSwitch, VMware vSwitch (presumably also OVS based) and RedHat if they would ever make a vSwitch. Guessing the 1000v is out oO
Figure 1. I freely admit, I loved this graphic on the homepage of their site.
Figure 2. Heavy emphasis on networking services such as load balancing and firewalling.
Vyatta Network OS Highlights
- Advanced IPv4 and IPv6 routing (BGP Multipath, PBR, OSPF)
- Stateful firewall
- IPv6 compatible
- Linux-based extensible network OS
- IPSec & SSL-based OpenVPN
- Secure Web filtering
- VMware, Hyper-V, Xen/XenServer, Red Hat KVM Ready
- Restful API, CLI, Web GUI
Vyatta for x86 Servers
The roots of Vyatta are from a project called XORP (for eXtensible Open Router Platform) a routing engine developed on Debian and funded by Intel and the National Science Foundation (NSF) in 2002. At its roots it is software routing on x86 hardware. They refer to this architecture as vPlane.
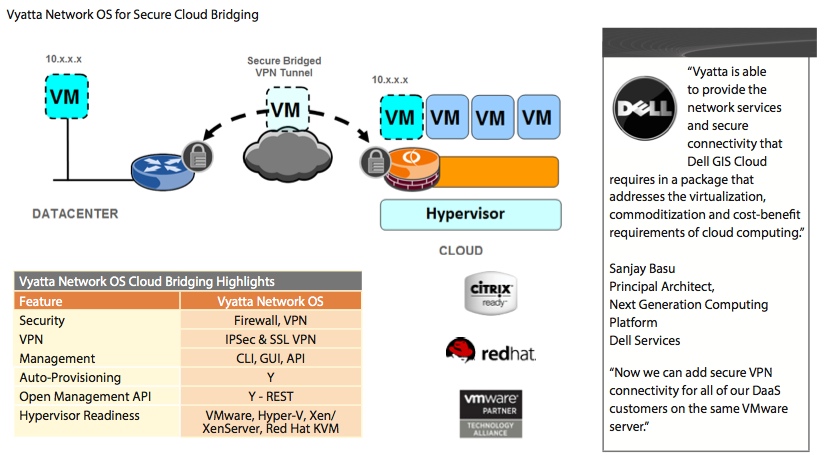
Figure 3. This looks like some familiar SDN territory, layers, abstraction, APIs, decoupling etc.
From the FAQ:
Vyatta vPlaneTM is a distributed Layer 3 (L3) forwarding plane that is architecturally separate from Vyatta’s network controller. The vPlane technology runs on individual x86 cores and takes advantage of the latest Intel advances related to networking performance. With this architectural separation, vPlane will allow Vyatta to deliver an order of magnitude faster forwarding performance that can scale linearly with the number of available x86 cores.
Here are the features of vPlane. Notice the caveat of “small packet sizes” that is significant.
- Near line-‐rate 10Gb/s throughput at small packet sizes to leverage the new era of 10Gb/s servers
- Physical de-‐coupling of forwarding plane from control plane
- Full interoperability with existing network infrastructure
- Ability to accommodate new protocols such as OpenFlow
Here is a snippet of what the configuration looks like. It is the C bracketed look of JunOS.
|
1 2 3 4 5 6 7 8 9 10 11 12 |
vyatta@R2# show interfaces wireless wireless wlan0 { address dhcp security { wpa { passphrase "Test phrase" } } ssid Test type station } |
There is also quite a bit of reference material for data center interconnects.
Figure 4. The DCI from one colo to another. Dell was referenced quite a bit as a user, would allude to some courtship there if I were to guess.
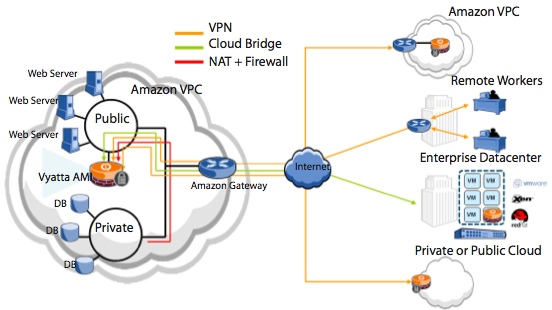
Vyatta for Amazon
Brocade recently demoed OpenStack Quantum integration recently at Network Field Day #4 which can be viewed here. I would take a guess that a long term strategy will be to get the same level of integration they have in the Amazon Cloud into OpenStack. I could see some use cases for hybrid cloud needs for advanced networking such as tunneling and crypto where having a software interface capable of tunneling could be handy. That said I can do that with OVS as I have done in a post a while back with the HP Public Cloud here.
Figure 5. How this solution integrates into the public cloud.
The true integration into the hypervisor means having primitives into the vSwitch on the hypervisor. They will need to rely on partners for that outside of the open source realm.
My Two Pennies on Vyatta
What Vyatta represents to me is using x86 hardware in as a swiss army knife to networking. Today if you need load balancing you buy a load balancer, if you need security you buy a firewall, if you need, well you get the point. Provisioning services until recently meant hoping the budget can absorb the purpose built hardware you are going to need. There are certainly benefits of custom and commodity ASICs, NPU, TCAM etc, but it comes at a cost and with constraints. That said am I staking my mortgage payment on x86 networking today? Eh, but in the coming years as software and reference architectures continue to mature I think x86 networking on the edge has a place. Applications controlling the network will become much more interesting in coming years as scalable solutions are worked through, security is beginning to become an early such play because to date, most solutions are either cost prohibitive network wide or are hacked together by really smart ITSec folks.
If you look at many shipping products today, especially in security or services routers markets, those are silicon with loads of embedded cores. Chip makers are beginning to deliver processors optimized for L7 payload inspection. The ability to RegEx and presumably re.sub() without the traditional performance penalty is becoming realistic. The Broadcom XLP 200-Series Multicore Communications Processor line demonstrates the vendor demand from foundries for application awareness.
Probably the most interesting dynamic is between VMware, Cisco and Brocade with this acquisition. I didn’t even know about the CSR and was quite peeved at that, until Network Field Day #4 in October that I was honored to be a part of which can be viewed here.
Greg Ferro already captured some of the impact (which I highly recommend reading) that filled in many blanks for me in a post at NetworkComputing. Prior to the acquisition they were certainly looking to cut into Cisco margins based on this document. I doubt Brocade bought Vyatta to cannibalize their own hardware sales so my guess is the idea of replacing enterprise routers and firewalls will fade, but hey there are significantly higher margins from software sales. Kudos for Brocade not un-publishing all of the documents on the Vyadda website so a nerd like me who needs a new hobby can read up.
All in all, I think the acquisition complements Brocade’s existing data center fabric products and their bullish approach to OpenFlow support in their hardware.
Vyatta references for this article:
Control Security, Connectivity and Compliance in the Amazon Cloud
Vyatta System High Availability Reference Guide
P.S. Can someone get the word “Virtualized” added to the universal keeper of spell checkers?
Thanks for stopping by!


I just replaced my software firewall with a Vyatta VM. It’s not too bad. Anyone familiar with JUNOS will feel right at home as the syntax is similar in many ways. It’s nice and light too, only requires about 2 GB of disk space, runs perfectly fine with 1 GB of vRAM (I can probably get away with less, this is just what I started with.)
The other interesting thing is its support for Wifi. Doing a bit of googling, I found a few do-it-yourself guides using cheap white-box WAP’s where you can replace the OS with Vyatta — not too bad of a deal if you’re looking for a cheap WAP that supports L3 and other features you wouldn’t typically find on the Wal Mart specials. Some definite potential for various networking DIY projects.